Key duplicate near me sets the stage for this narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset, allowing easy lock access without the need for spare keys.
The significance of key duplicates in daily life cannot be overstated. Not only do they provide a convenient solution for lock access, but they also play a crucial role in personal security and convenience. Whether it’s a spare key for a home, a business, or a vehicle, having a duplicate key nearby can be a lifesaver in case of an emergency.
Understanding the Significance of Key Duplicates in Daily Life
In today’s fast-paced world, key duplicates have become an essential component of our daily lives. From securing our homes and workplaces to granting access to our families and friends, key duplicates play a crucial role in granting us a sense of convenience and security.
When it comes to personal security, key duplicates can have a significant impact. Having multiple keys to our homes or offices can be a lifesaver in emergency situations, such as getting locked out or experiencing a power outage. Key duplicates can also be especially useful in situations where we have limited access to our regular keys, such as during a move or when we have a spare key in a secure location.
Scenarios Where Key Duplicates are Particularly Useful
Key duplicates are particularly useful in various scenarios, including:
-
Emergency Access: In emergency situations, such as a power outage or a medical emergency, key duplicates can grant quick access to our homes or offices, ensuring our safety and well-being.
-
Convenience: Key duplicates can be used to grant access to our homes or offices to family members, friends, or guests, eliminating the need for a physical presence to provide keys or to wait for access.
-
Security: Key duplicates can provide an additional layer of security, as they can be used to grant access to specific areas or rooms within a premise, limiting access to authorized individuals.
Key duplicates can also be useful in various professional settings, such as:
Professional Settings
Key duplicates are particularly useful in various professional settings, including:
-
Shared Office Spaces: In shared office spaces, key duplicates can grant access to specific areas or rooms, ensuring that only authorized individuals have access to sensitive information or equipment.
-
Service Providers: Key duplicates can grant access to service providers, such as electricians, plumbers, or maintenance personnel, ensuring that they can perform their tasks without requiring a full physical presence.
-
Security Personnel: Key duplicates can grant access to security personnel, ensuring that they can respond quickly and effectively in emergency situations.
Psychological Factors Influencing Reliance on Key Duplicates
Our reliance on key duplicates is influenced by various psychological factors, including:
-
Social Norms: The practice of using key duplicates is a social norm, with many people relying on them to grant access to their homes and workplaces.
-
Personal Habits: Our personal habits, such as carrying a spare key or keeping a key in a secure location, influence our reliance on key duplicates.
-
Convenience and Security: The convenience and security provided by key duplicates make them an attractive option for many people.
Key duplicates have become an essential component of our daily lives, providing convenience and security in various situations. By understanding their significance and the psychological factors influencing our reliance on them, we can better appreciate the importance of key duplicates in our daily lives.
Ensuring Authenticity and Legitimacy of Key Duplicates
In today’s security-conscious world, having a genuine key duplicate is not just a matter of convenience, but also crucial for ensuring the safety and integrity of your belongings. With the rise of key duplication services, it’s becoming increasingly important to verify the authenticity of key duplicates to avoid potential security risks.
The authenticity of key duplicates is a critical factor in maintaining the security of your property. A genuine key duplicate is one that has been created by a authorized person, using the correct procedures and equipment, to ensure that it functions perfectly and doesn’t tamper with the original key in any way. When a duplicate key isn’t created authentically, it can lead to security breaches, loss of valuable items, and even put people’s lives at risk.
Role of Unique Key Identifiers
A unique key identifier is a special code or marking assigned to each key, which serves as a verification tool to confirm the legitimate origin of the key. The unique identifier helps identify the exact key that corresponds to a specific lock, thus ensuring that only authorized individuals have access to the key and the lock.
The benefits of using unique key identifiers include improved security, reduced risk of unauthorized duplication, and increased convenience. Unique identifiers enable users to track the origin and history of their keys, making it easier to monitor and manage access to their property. This technology also promotes accountability and ensures that only authorized personnel have access to sensitive areas or valuable assets.
Characteristics of Genuine Key Duplicates
To ensure the legitimacy of key duplicates, look for the following characteristics:
- Correct key shape and size: A genuine key duplicate will have the exact shape and size of the original key, ensuring a perfect fit in the lock.
- High-quality materials: Genuine key duplicates are made from high-grade materials, such as metal or advanced polymers, which guarantee durability and performance.
- Accurate key blank: A genuine key duplicate is made from an authentic key blank, which provides the precise specifications and characteristics of the original key.
- Authorized manufacturer mark: A genuine key duplicate is manufactured by an authorized company, with a clear and visible mark indicating the manufacturer’s name and logo.
A genuine key duplicate is a critical component of a comprehensive security system, ensuring that your property is protected from unauthorized access and potential security breaches. Always choose a reputable key duplication service that adheres to industry standards and regulations to ensure that your key duplicates are authentic and reliable.
Best Practices for Key Duplicate Management and Disposal: Key Duplicate Near Me
Safe handling and disposal of key duplicates require strict adherence to protocols that balance security, environmental responsibility, and organizational efficiency. Proper key management not only mitigates potential security breaches but also ensures regulatory compliance and minimizes the risk of unauthorized access.
Effective key management systems involve several components, including key storage, labeling, and disposal protocols. A structured approach to managing key duplicates is crucial for businesses and individuals alike to prevent unauthorized use or disclosure of sensitive information.
Key Storage and Access Control
Key storage and access control are critical factors in maintaining the security of key duplicates.
The following table Artikels the key best practices for storing keys securely:
| Secure Storage Location | Keys should be stored in a locked cabinet or safe with restricted access. |
| Labeling and Tracking | Keys should be properly labeled, identifying their intended use, and each duplicate should be assigned a unique tracking code. |
| Password Protection | Password-protected storage devices and electronic files containing key information should be used to prevent unauthorized access. |
| Limit Access | Access to key storage locations and electronic files should be strictly limited to authorized personnel and should be properly monitored. |
Key Disposal
Proper disposal of key duplicates is essential to prevent unauthorized access, maintain data confidentiality, and protect the environment. When disposing of key duplicates, consider the following best practices:
Environmental Responsibility and Compliance
Compliance with regulatory requirements and minimizing environmental impact should be a primary concern. Key duplication and storage operations should adhere to the following principles:
Securely shredding or destroying key duplicates is a recommended method for ensuring environmental responsibility and compliance with data protection regulations. Key disposals should also be documented to maintain transparency and accountability.
Secure key disposal methods include:
- Physical destruction using shredders or cutters
- Burning or incineration of key duplicates in secure facilities
- Electronic destruction through secure data erasure programs (overwriting or degaussing electronic media)
Key Management Systems, Key duplicate near me
Key management systems involve a combination of policies, procedures, and technologies that maintain accountability for key access, use, and storage. A properly implemented key management system ensures compliance with security and regulatory requirements, reduces the risk of unauthorized access, and enhances organizational efficiency.
Common key management systems include:
- Centralized key management software that integrates all aspects of key management
- Hardware-based key management systems, such as secure key cabinets or vaults
- Hybrid systems that combine centralized software with hardware-based storage solutions
Key management should be integrated with organizational policies and procedures to optimize efficiency and minimize the risk of security breaches.
Overcoming Challenges in Key Duplicate Creation and Use
The process of creating and using key duplicates can be intricate, and various challenges may arise. These difficulties can stem from a range of factors, including issues with key duplication equipment, user error, or lack of proper documentation. To overcome these challenges and ensure seamless key duplication, it is crucial to understand the potential hurdles that may be encountered.
Various users may face problems while creating or using key duplicates. For instance, users may struggle with key duplication equipment malfunctions, difficulty in selecting the correct key blank, or inaccurate key duplicating techniques. These issues require immediate attention to resolve and ensure the creation of accurate and functional key duplicates. Understanding these challenges and developing effective troubleshooting strategies can significantly improve the overall key duplicate creation process.
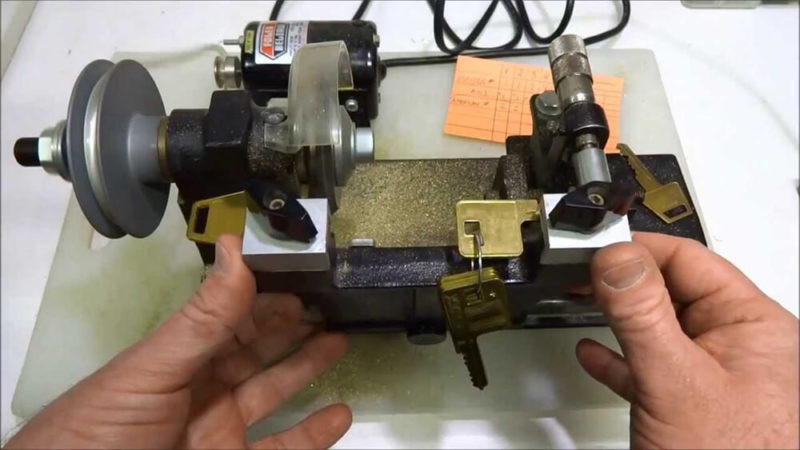
Common Issues with Key Duplication Equipment
Inadequate key duplication equipment or insufficient user knowledge can lead to various problems during the key duplication process. To address these challenges, it is essential to identify common equipment-related issues and develop troubleshooting techniques to rectify them.
Some of the most common issues with key duplication equipment include:
- Malfunctioning key duplication machines: These machines may require routine maintenance, proper calibration, or replacement of worn-out parts to ensure accurate key duplication.
- Inadequate key blank selection: Users may struggle to select the correct key blank, leading to inaccurate key duplication. This can be mitigated by ensuring users have access to comprehensive key blank catalogs and understand key duplication principles.
- Insufficient user training: Inadequate training or lack of experience can lead to user error and inaccurate key duplication. Providing comprehensive user training and offering regular equipment maintenance can help address this issue.
- Environmental factors: Extreme temperatures, humidity, or dust can affect key duplication equipment performance. Maintaining a clean and controlled environment can minimize these issues.
Different Types of Key Duplication Services
The effectiveness and cost-effectiveness of key duplication services can vary depending on several factors, including the type of equipment used, user expertise, and the complexity of the key duplication process. Understanding these differences can help users select the most suitable key duplication service for their needs.
Some common types of key duplication services include:
- On-site key duplication services: These services involve a technician visiting the location to create key duplicates. This option is ideal for large businesses or organizations that require multiple key duplicates.
- Key duplication centers: These centers specialize in key duplication and offer a wide range of services, including key cutting, key blank selection, and key duplication machine maintenance.
- Distribution centers: These centers provide key duplication services to local businesses and organizations, often with a focus on speed and efficiency.
Closing Notes

In conclusion, the use of key duplicates near me offers a safe and convenient solution for lock access. With the right understanding and practices, individuals can enjoy the benefits of key duplication without compromising on security or convenience.
Essential FAQs
What is key duplication?
Key duplication is the process of creating a copy of a key, which can be used to access a lock or a set of locks. This is typically done for convenience and security purposes.
How do I find a key duplicator near me?
You can search online for key duplicators in your area or check local directories for listings of locksmiths and key duplication services.
What are the benefits of having a key duplicate near me?
Having a key duplicate near you can provide a convenient and safe solution for lock access in case of an emergency or if you forget your keys.
Can I use a key duplication service for other types of keys?
Yes, many key duplication services can work with various types of keys, including house keys, car keys, and business keys.